You Are Not YOU. Now What?
When your identity is stolen, sheer panic sets in. How bad is it? How did they get your information? How much information do they have? How much damage has been done? What do you do now? How long will it take to stop this? Those are often the first questions that pop into your mind.
A quick search on Google will give you a Basic To-Do List, and it’s just that… B-A-S-I-C: (1) File a report with the Federal Trade Commission and (2) Put an alert on your credit files with the Big 3 (I already had one).
Whoop-dee-doo.

The problem is the criminals already have your information, and they have it not just for today but forever and ever and ever. But wait, there’s more! They can sell it on the dark web to others who can mess with your identity as well. And the thieves are patient because the payoff can be very lucrative. But it goes much deeper than charging things under your name. These criminals can do damage way beyond your credit profile, and you may not find out the depths of their activities until much later.
For instance, they can use your identity to:
- open online bank accounts (a deposit account) with no money, your credit isn’t pulled, so security freezes and fraud alerts on your Experian, Equifax, and TransUnion accounts do absolutely no good if a lender or financial institution doesn’t pull your credit report
- file for a tax refund on your behalf, you won’t know about it until you file your taxes
- provide false documentation to people working illegally in the country who will then file their wages with their employer under your tax ID number, and your tax ID number will show all that additional income earned you never knew about (and who pays those taxes?)
- make a driver’s license in another state for someone else (if they are in an accident, does it go on your record or insurance?)
- hijack and clone your cellphone, giving them access to a myriad of personal information, log-ins, passwords, contacts, photos, apps including your home security app, biometrics data, and more!
So what do you do when you get that letter that someone has opened up a fraudulent bank account in your name?
While I’m sure there are even more, HERE ARE THE 18 STEPS I discovered that needed to be done after this happened to me. Do them! Even if they seem futile:
- Go to the Identity Theft section of the FTC website to report the theft. You will be given an account number and a personalized checklist of things to do. To avoid more scams, ALWAYS be mindful of websites you visit including their extensions. Government websites will have a .gov extension, not a .com extension.
- Fill out a police report with your local police department. Often, the local police will tell you they can’t do anything about something that happens online. That’s true, but these criminals have your personal information and may be closer than you think. Don’t immediately assume they are in another untouchable country. Also, the credit bureaus require a police report to any extended fraud alerts.
- Contact the three credit bureaus and have them add a (1) permanent security freeze to your account and (2) a 7-year fraud alert. If you like to use credit cards and open accounts, this will mean you will have to plan ahead to temporarily unlock your security freeze to apply for credit or buy a car. In the long run, though, it’s well worth protecting yourself. Keep in mind that just because you have a credit freeze and people may not have access your credit account, they can still open deposit accounts or no-credit-check accounts in your name. When searching online for your free credit reports, be aware of companies posing as the official website in an attempt to have you sign up for other services. The FTC website states the official website where you request your annual report is called AnnualCreditReport.com, and you will be able to access ALL THREE reports in one place. If you need to contact them individually, here’s their info:
- Equifax.com/personal/credit-report-services | 800-685-1111
- Experian.com/help | 888-397-3742
- TransUnion.com/credit-help | 888-909-8872
- Add verbal passwords to all of your bank accounts by phone in addition to any PIN numbers. It’s best to contact your bank through their mobile app so they can verify you that way before the conversation begins. Tell your banks, credit unions, and lenders of home equity lines of credit that you have had your identity stolen, and you want to add additional layers of security. Enable text or email notifications as well as additional authentication methods. Change ALL of your log-in information including user name, password, and security questions. Only use ISP based emails instead of vanity emails that are forwarded to a real internet service provider (see #7). This means don’t use a gmail, aol, yahoo, or other cloud-based email for banking! This also means DON’T forward your ISP to a cloud-based email!
- You will need to do two things with the Social Security Administration. First, go online to the website and block access to your account immediately. Second, visit your local Social Security office in person (yes, it can be a long wait) and tell them what happened. They will check to see if anyone has tried to file on your behalf if you are eligible for benefits now. If you are not eligible, they will provide you with printed instructions and two security codes so you can create your new account when you get home. They won’t issue you a new social security number unless yours in an extreme case because there are additional headaches with that resolution.
- Call your wireless cellphone provider and tell them you want additional security with a verbal password beyond the PIN they have on file since your identity was stolen. If the thieves can hijack your phone, that’s another level of ugly as they could potentially get access to all of your banking and other secure apps.
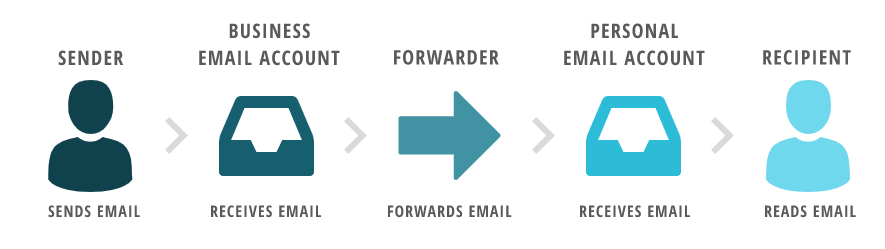
- If you are using email forwarding, add protection to your email account. Why? When you need to reset your password, most websites will send you password reset instructions to your email account. If you use a hosted email provider like GoDaddy, Bluehost or Microsoft Office and forward your emails to your IP provided email account, you need to add additional security to your email account so the criminals don’t try to redirect your emails and hijack all your accounts before you can change it. There may be a fee for additional security with the hosted email providers. Read more about the cons of email forwarding from Kevin Pryce’s blog.
- If you don’t have a computer security program such as Norton, McAfee, or other program, BUY IT NOW. Period. Some come with a password vault, so consider that when reading the next point below.
- Audit all of your online accounts.
- Log in to your Google account, change your password, add as much authentication as possible. Access to your Google account means they can access your private Google docs, photos, databases, and all other personal information you don’t know Google has stored for you (think about it… Google is working to get into the healthcare info sector!). BTW, you know Gmail isn’t secure, right? Ok, enough of that.
- Access to your Google account also means they have access to your passwords if you save them on your computer! Check your Google Password Manager for a list of accounts you will need to update. You can search for reviews on some of the top non-Google based password vaults and read how they secure your data, if it doesn’t come with your security program. The jury is out on if an online password manager or vault is better than writing it down in a journal. Personally, I think a journal has much less of a chance being stolen from your home than your computer getting hacked, but if you live in a place where break-ins are common or share space with roommates, you will need to determine the best course of action in your situation.
- Anyplace – that’s a-n-y-p-l-a-c-e – you have a profile online, change ALL of your log-in information (username, password, security questions) and delete credit card or other payment information on ALL of your online accounts, even expired cards. Deep dive inside your computer, bookmarks, and history to see what online accounts you have that may have access to credit cards, even if they are old. Are they an http site instead of https? Have you used a travel website to book a flight, hotel, or car? If you don’t use an account or service anymore, delete the information from it or delete the account altogether. Use unique userIDs for each website and not something that’s easy to figure out if a hacker jumps from one site to another.
- Create LONG & STRONG passwords. Don’t use anything remotely similar to past usernames and passwords as criminals can run your information through software hacking programs to make logic-based and patterned guesses based on information they have on you (remember those cute Facebook quizzes you filled out years ago about your childhood best friend’s name and shared with all your friends?). Make your password as long as you can – 26 characters is a good start, if the site will let you. Use a combination of upper and lower case letters, numbers, and symbols. Stay away from common phrases, dates, or names you use or say as criminals can access your social media accounts (yes, change the login information on your social media accounts). BTW, criminals know that substituting 3 for “e”, or ! for I, and @ for “a” are common, so you can bet it’s part of their software hacking algorithm. Below is a screenshot on what information hackers are gathering on their victims to customize their scams:

- Tell your employer’s Human Resources department in case the criminals pose as you and ask HR to help you change your direct deposit to that new fake account they created in your name. [Real life example here, folks!]
- Call your healthcare providers and let them know your ID was stolen. Many providers will be able to add a verbal password to your account in case someone tries to gain access to your medical records.
- Call your pharmacy as they can transfer your medications to another pharmacy, pay for them with that account they opened in your name, and sell the drugs on the street. [In my case, my pharmacy photocopied the driver’s licenses of anyone I approved to pick up medications on my behalf and would check ID each time a prescription was picked up.]
- Contact your CPA to file a tax return ASAP and inform them that your identity has been stolen. If you don’t have a CPA, it’s worth the effort to get their assistance in this area. If it’s tax time and you expect a refund, file your taxes immediately because “the first one to file gets the refund!” You will also know when you go to file if someone has already filed in your name. You can make changes to your tax return a little later (which is why it’s a good idea to hire a CPA if your identity has been stolen).
- Set your social media networks private and begin removing people you don’t know. It’s likely these criminals have already found you online and have your picture, which they can use to try and intercept information as well.
- In addition to credit bureaus, did you know that there are also checking account bureaus (the link is a PDF of company contact info)? These companies track negative activity as it relates to checking accounts. You can get a free checking activity report by contacting nationwide checking account reporting companies to see if any checking accounts have been open in your name:
- Certegy Check Services 800-237-3826
- ChexSystems
- CrossCheck 800-843-0760
- Early Warning Services 800-327-7775 (option 4)
- TeleCheck Services
- Put security freezes with companies that focus on subprime consumer market loans (payday loans, installment loans, auto loans, check cashing services, rent-to-own transactions, etc): ClarityServices.com
- Contact your local DMV. While my effort was futile, yours may not be. Since the drivers’ license agencies are run by state agencies and have different systems, it likely won’t do much good to sit in line at the DMV to alert them to any identity theft if someone twelve states away is getting a driver’s license. See if there is a phone number to call instead (Google “drivers license fraud [your state]”). My conversation with the NC DMV confirmed that the DMV has systems in place should someone try to get a license in NC under false pretenses, but beyond the state borders, they don’t have fraud alert capabilities to post on individual accounts. In 2020, the Real ID license is required, so fraud with the DMV may be less of a threat.
- File a report with the Internet Crime Complaint Center (IC3). While I don’t really know what they will do specifically for your case, all the government agencies recommended filing a report. Perhaps they will assemble a task force to cut off the dragon’s head.
While hackers may have some information on you already, they could be still working on building your profile as you read this by searching the web for additional information from less secure sights. Be paranoid! Work to get control of your personal information now before a criminal gets even more. The more info they have on you, the more convincing they can be that THEY ARE YOU, and YOU ARE NOT YOU.
What else you should know
ABOUT PASSPORTS: For my situation, I contacted the U.S. Passport office about scenarios that would deal with faking or accessing my existing passport. They referred me back to the FTC who referred me to the U.S. Passport office. Neither agency could help. Lesson assumed: if you travel in anyway shape or form, you may want to go ahead and claim your passport now.
Can LifeLock or another security provider help you recover?
While many of what they offer is of some value – they will fight on your behalf – my own experience was that it was up to Me, Myself, and I. [BTW, when you sign up for LifeLock, they want your full social security number and other personal info, so how will they prevent their own company from getting hacked as criminals get more and more sophisticated?]
I was the one who had to go IN PERSON to the banks, Social Security Administration, the pharmacy, etc., and prove my identity to get the security measures placed on my specific accounts. When filing a police report, they came to my home.
And quite honestly, I am not sure I want anyone else knowing one more bit of information about me, especially a verbal password that is customized for my interactions with a bank.
How did they get your information?
Who knows? If someone has your social security number, they got it from someplace like a bank, lender, healthcare provider, government or other organization who has your personal private information (PPI) and hasn’t locked down their system well at some point in time.
It may have been Equifax, Target, Capital One, Anthem (formerly known as WellPoint), eBay, JP Morgan Chase, Yahoo, Marriott, Home Depot, Adobe or even a lesser known breach… or any combination of the lot.
Think about who needs your SSN and why. Did you apply for a job online and provide your number? Why do you need to provide a company with that level of information before the interview even takes place?
SIDEBAR REGARDING THE EQUIFAX BREACH: Equifax only notified people by email, not by US postal mail, because of the extreme number of people impacted. Apparently, federal regulations state that if a security breach happens to a humongous amount of people, the company doesn’t have to contact them directly. Instead, they set up a website and make YOU go fish for your information – as if you want to go to a website that was hacked previously and enter your information in there.
Through this ordeal, a question was posed by several different people, and I don’t think it is as sarcastic as it used to be:
“Do you really think all of your very personal information is NOT already somewhere on the Dark Web?”
What are they going to do with your profile now?
We know they want money, and this is typically considered a non-violent crime, so what’s the big deal, right? These are typically sophisticated networks of technologically skilled thieves who have may just want money or they could have another agenda:
- supporting nation state terrorism
- human trafficking/slavery
- sex trafficking/slavery
- drug cartels
- illegal immigration
- child pornography rings
- and a host of other vile crime
Whether it’s a challenge or akin to a video game, builds their ego, or they are just criminals by nature, they are all the same – thieves, crooks, corrupt individuals who deserve to be removed from society without access to technology for the remainder of their lives.
Identity Theft is not Credit Card Theft
Identity Theft is when the criminals have your personal information and can pretend to be you to gain access to your money or to commit crimes and fraud. Credit card theft is when criminals have access to just your credit card information and begin charging to your account. If you’ve had your credit cards stolen, you may benefit from taking additional steps to prevent your identity from being stolen as well.

You must be logged in to post a comment.